Optimizing SPI communication on STM32 MCUs: a comprehensive guide to high-frequency communication
Published at July 28, 2023 ·
Artur Kowalski
·
22 min read
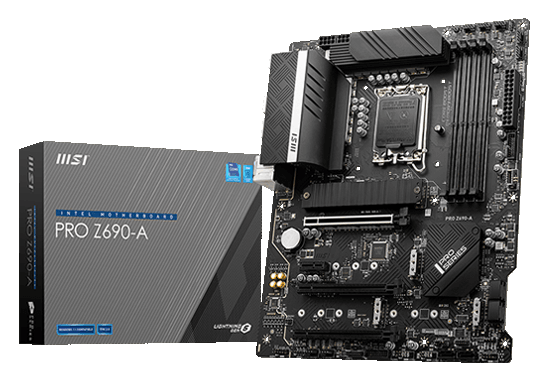
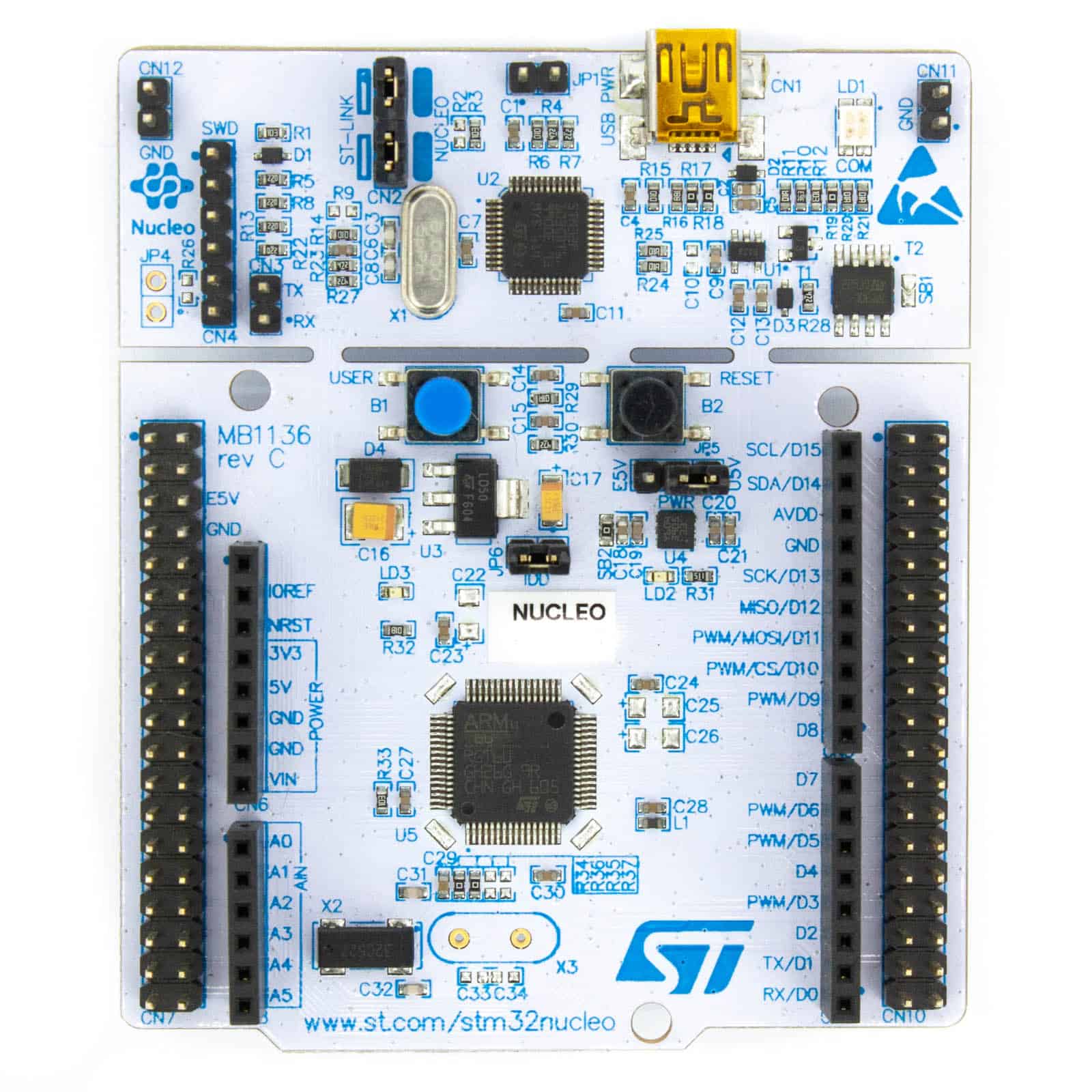
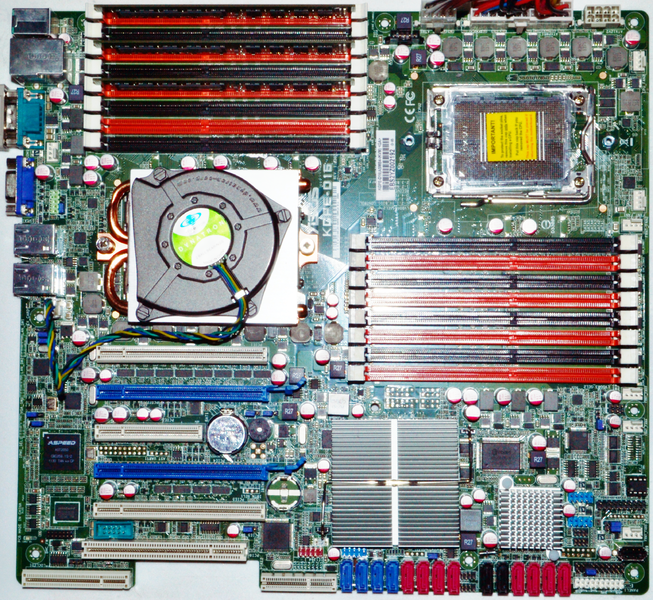
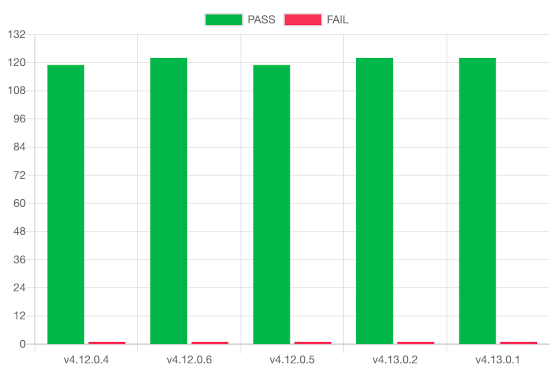
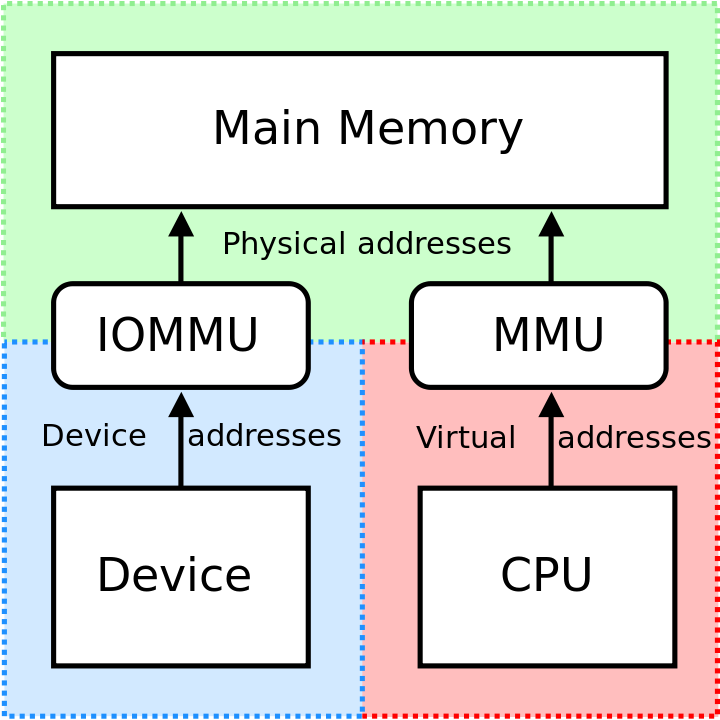
In this blog post, we delve into the fascinating world of Serial Peripheral Interface (SPI) on STM32 microcontrollers (MCUs). Specifically, we explore how SPI is utilized in TPM chips for communication with PC motherboards. We encounter the challenges of achieving high-frequency SPI communication, especially when operating as a slave, and the specific limitations of STM32L476 MCUs. The article further uncovers the limitations of existing approaches in platforms like Zephyr and STM32 HAL. We then embark on a journey to fix SPI issues, improve DMA performance, and optimize the firmware for high-speed SPI communication. Throughout the blog post, we provide in-depth technical insights and share valuable test results. Join us as we push the boundaries of SPI communication and unlock new possibilities in the world of microcontrollers....
Categories:
firmware
miscellaneous
security